Презентация Cybersecurity онлайн
На нашем сайте вы можете скачать и просмотреть онлайн доклад-презентацию на тему Cybersecurity абсолютно бесплатно. Урок-презентация на эту тему содержит всего 65 слайдов. Все материалы созданы в программе PowerPoint и имеют формат ppt или же pptx. Материалы и темы для презентаций взяты из открытых источников и загружены их авторами, за качество и достоверность информации в них администрация сайта не отвечает, все права принадлежат их создателям. Если вы нашли то, что искали, отблагодарите авторов - поделитесь ссылкой в социальных сетях, а наш сайт добавьте в закладки.
Презентации » Интернет » Cybersecurity
Оцените!
Оцените презентацию от 1 до 5 баллов!
- Тип файла:ppt / pptx (powerpoint)
- Всего слайдов:65 слайдов
- Для класса:1,2,3,4,5,6,7,8,9,10,11
- Размер файла:4.35 MB
- Просмотров:103
- Скачиваний:8
- Автор:неизвестен
Слайды и текст к этой презентации:
№12 слайд


Содержание слайда: Who are the cybercriminals?
Crackers and Hackers
Computer-savvy programmer who create attack software
Script Kiddies
Unsophisticated computer users who know how to execute programs created by the crackers
Criminals
Create & sell bots to generate spam
Sell credit card numbers, etc…
№19 слайд


Содержание слайда: Offensive Content or harassment
The content of online information may be distasteful, obscene or offensive for a variety of reasons
Hate speech
Against a group based race, religion, ethnic origin, disability, etc.
Harassing someone through cyberspace
Stalking, threats of violence, cyberbullying
№22 слайд


Содержание слайда: Cybercrime Summary
Cybercrime is any criminal activity carried out using computers or the internet
Cybersecurity is taking measures to protect a computer from unauthorized access
Cybercriminals exploit others for their personal gain
Cybercrime categories: Computer as a tool, as the target, selling illicit goods, offensive content and harassment
Computer as a tool: When an individual is a primary target
Computer as a target: When a computer is a target
№24 слайд


Содержание слайда: Learning Objectives
Define the goal of cybersecurity
Describe easy targets
Explain general guidelines of protection against cyber threats
Describe why pirated software is not safe
State why software updates are important
Describe the difference between a password and a passphrase
№26 слайд


Содержание слайда: Good Line of Defense
Can you prevent from being a victim of cybercrime?
If a professional hacker or government surveillance wants your information, they will get it.
Make them work them for it! In doing so, they might give up and move on to an easier target
Minimizes the chances of being a victim
№27 слайд


Содержание слайда: Password Cracking Example
Hackers use “Brute-Force” Password Crackers
One group cracked 2700 “bad” passwords in 30 seconds
The crack program ran for 48 hours more and did not crack the 250 remaining “good” passwords
Do the hackers keep trying to get the remaining 250 passwords? Or do they find easier targets?
Your goal: Be one of the 250
№33 слайд


Содержание слайда: Pirated Software (2): Created by Criminals
Crackers hack software for a living
They do not do it for the goodwill of the community
They are not Robin Hood
If they crack software, they do so to help their criminal enterprise
They can control the computers of those who install it
№41 слайд


Содержание слайда: Passwords (2): Passphrase
Use a passphrase if you need to memorize your password
Strong passwords require a password safe
Memorize a passphrase (can use special letters)
Positive message: I want 2 smile more :)
Random words: Yellow-green pancakes 4bfast
Some phrase: Te@ is better with milk
A memory: Remember Turkey 2017?
№42 слайд


Содержание слайда: Final point to ponder
Someone will always have your data
You give them permission to read the emails and your documents by using the service
Do you trust them?
Who do you trust more not to abuse your data?
mail.ru/.kz
Gmail.com
yandex.ru/.kz
any-email-address /.com/.ru/.cn/.eu/.abc
№43 слайд


Содержание слайда: Cybersecurity Summary
Goal: Be a difficult target
Easy targets: People with a low awareness of cybersecurity; don’t take measures to protect themselves online
Protection guidelines: Use official software that automatically updates, do not visit shady websites, and choose strong passwords
Pirated software: Are tools of hackers
Software updates: Fix recent exploits in software
Password: UecX6JxZJ^cJ$;
Passphrase: I like d33p blue!
№50 слайд


Содержание слайда: Malware (4): What They Do
Worms self-replicate but do not cause harm
Viruses can cause the computer crashes, loss of data,
Trojan horses steal data and provide a backdoor for the cybercriminal
Spyware collects data from the infected machine
Keyloggers record all of a user’s keystrokes
Fake antivirus software allows malware to remain undetected
This is true for pirated/hacked antivirus software
№53 слайд


Содержание слайда: Malware (7): Protect Against
Use a reputable antivirus program
Keep your computer up to date
Do not visit untrusted websites
Do not click unknown links in an email
Do not download files from unknown sources
Do not use pirated software
Most pirated software contains malware
№62 слайд


Содержание слайда: Unsolicited Email (2): Click Here
If you click a malicious link or fall for a phishing scam, it might be too late…
Drive-by downloads: Malicious software can install just by visiting a website (virus, ransomware, keylogger)
Ransomware: 93% of all phishing emails are now ransomware
№63 слайд


Содержание слайда: Unsolicited Email (3): Protection
In addition to the malware protection guidelines:
Know how to identify fake email or spam
Never click a link in an email, not even from a friend, unless you know it is safe
Never click a password reset link. Instead, go to the website directly
Mouse over a link to verify the URL
№64 слайд


Содержание слайда: Open WiFi Access Points
Any data transmitted through an unsecured WiFi connection can be easily collected
Intercepting login credentials
Only use SSL/HTTPS when logging into your sites
Understand the risks and use with care
Virus threat from infected users
Better to use mobile data through your phone
№65 слайд


Содержание слайда: Common Threats Summary
Common cyber threats
malware, data leaks, unsolicited email, and public WiFi
Malware is malicious software that runs the background
From: untrusted websites, email attachments, pirated software, infected flash drives, or infected computers on a network
Data leaks publish private data online
Harmful websites automatically install malware when visited
Public WiFi expose unencrypted data, such as passwords
Скачать все slide презентации Cybersecurity одним архивом:
Похожие презентации
-
 Техніка безпеки. Електронна пошта. Урок 1
Техніка безпеки. Електронна пошта. Урок 1 -
 Топ 10 сайтов
Топ 10 сайтов -
 Залогинивание
Залогинивание -
 Концепция сайта кафе Авокадо
Концепция сайта кафе Авокадо -
 Правила участия в скайп-конференциях
Правила участия в скайп-конференциях -
 Информационная кампания для родителей (законных представителей) ДДЮТ
Информационная кампания для родителей (законных представителей) ДДЮТ -
 Сервис Рука помощи на официальном сайте Череповца
Сервис Рука помощи на официальном сайте Череповца -
 Задача регистрации курсов (use case)
Задача регистрации курсов (use case) -
 Социальная сеть деловых контактов SkillsNet (www. SkillsNet. ru)
Социальная сеть деловых контактов SkillsNet (www. SkillsNet. ru) -
 Потребление в Интернете: преимущества и вызовы
Потребление в Интернете: преимущества и вызовы -
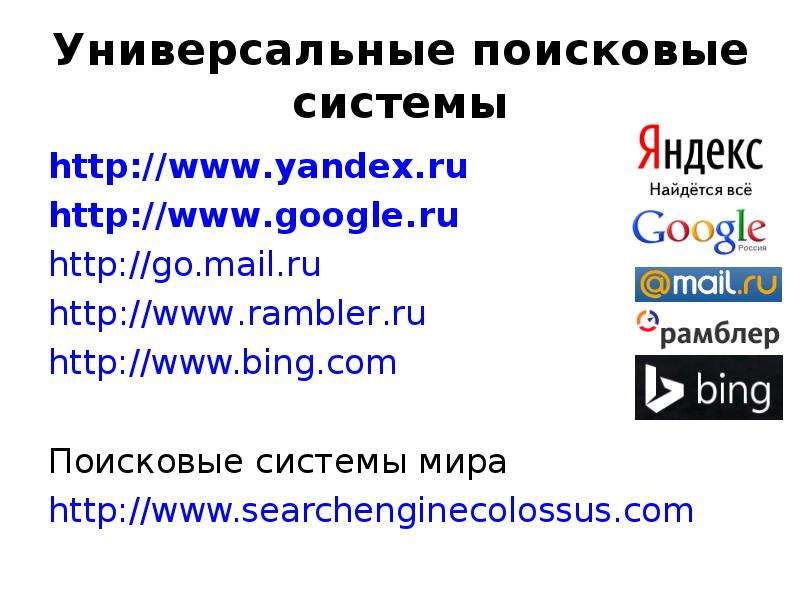 Универсальные поисковые системы
Универсальные поисковые системы
















































